Nonrepudiation PowerPoint PPT Presentations
All Time
Recommended
And the Lord God called unto Adam, and said unto him, Where ... Presentation of the matter before the arbiter of the dispute. Decision. 39. Dispute Resolution ...
| PowerPoint PPT presentation | free to view
Dispute arbitrator will likely give greater weight to evidence generated and ... wills and trusts, family law matters, much of Uniform Commercial Code (UCC) ...
| PowerPoint PPT presentation | free to view
????? ??????? ??? ?? ?? ?? ???? ?? ????? ????? ????? ??????? ????? ? ????? ??? ?? ???. ... Nonrepudiation. Integrity Control. ??? ????? ??????? ...
| PowerPoint PPT presentation | free to view
MSCS 282 - Topics in Computer Science: Advanced Database Systems. Team members ... Nonrepudiation. You can not deny your signatures SignatureValue ...
| PowerPoint PPT presentation | free to view
Chapter 30 Message Security, User Authentication, and Key Management 30.1 Message Security Privacy Authentication Integrity Nonrepudiation Figure 30.1 Message ...
| PowerPoint PPT presentation | free to download
... contents of message in a manner provable to a disinterested third party ('judge') Sender cannot deny having sent message (service is 'nonrepudiation' ...
| PowerPoint PPT presentation | free to download
... contents of message in a manner provable to a disinterested third party ('judge') Sender cannot deny having sent message (service is 'nonrepudiation' ...
| PowerPoint PPT presentation | free to download
... contents of message in a manner provable to a disinterested third party ('judge') Sender cannot deny having sent message (service is 'nonrepudiation' ...
| PowerPoint PPT presentation | free to download
Key management distribution of cryptographic keys, mechanisms used to bind an ... transmitted in the clear (must be encipher when sent or derived without an ...
| PowerPoint PPT presentation | free to view
... and a public key that is announced to the public (i.e. via the internet). The most common public-key algorithm is named after its inventors: Rivest-Shamir ...
| PowerPoint PPT presentation | free to download
Title: PowerPoint Presentation Author: Ninghui Li Last modified by: Ninghui Li Created Date: 6/16/2003 8:07:26 PM Document presentation format: On-screen Show (4:3)
| PowerPoint PPT presentation | free to download
As we’ve previously covered the difference between electronic signatures and digital signatures, using an esignature to sign agreements, contracts and similar sorts of documents is a great way to save time and money.
| PowerPoint PPT presentation | free to download
Centralised or Decentralised Controls. The Layer Below. G53SEC. 21. Focus of Control ... Centralised or Decentralised Controls. 4th Design Decision ...
| PowerPoint PPT presentation | free to download
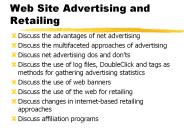
The Internet has become the largest marketplace in the world. ... Sometimes Advertising Agencies act as intermediaries (e.g. Overture) How to measure site visits? ...
| PowerPoint PPT presentation | free to view
E-Commerce Security ... E-Commerce
| PowerPoint PPT presentation | free to download
Lecture 8 Applications and demos
| PowerPoint PPT presentation | free to download
... a message is concealed by encoding it. The sender encrypts the message using a ... This technique only protects against unintentional alteration of the message ...
| PowerPoint PPT presentation | free to download
... of applications on an appliance. Security of transactions between applications ... Security protocols greatly increase computational requirements of appliances ...
| PowerPoint PPT presentation | free to download
Title: Information Systems Planning Author: desta.a Last modified by: mas01md Created Date: 1/5/2005 12:17:07 PM Document presentation format: On-screen Show
| PowerPoint PPT presentation | free to download
- Also called Symmetric encryption involves using the same key for encryption and decryption. One Time Pad: A Private Key Cryptographic Algorithms.
| PowerPoint PPT presentation | free to download
Markus Geissler, PhD Professor, Computer Information Science Cosumnes River College Sacramento, California, USA
| PowerPoint PPT presentation | free to view
TRAI * * * * * * * * Background Threats Present Status Challenges and Strategies * TRAI * Critical infrastructure means the computers, computer systems, and/or ...
| PowerPoint PPT presentation | free to download
In end-to-end encryption, each host shares a cryptographic key with each destination. In link encryption, each host shares a cryptographic key with its neighbor(s) ...
| PowerPoint PPT presentation | free to view
PENGANTAR KEAMANAN KOMPUTER Materi I Keamanan Komputer One_Z Peraturan utama Keamanan Komputer Pasal 1: Tidak ada komputer komputer yang aman. Pasal 2: Kalau ada ...
| PowerPoint PPT presentation | free to download
... the message according to an equation or algorithm into unreadable 'ciphertext'' 'Decryption is the translation back to plaintext when the message is received by ...
| PowerPoint PPT presentation | free to view
Money Gram, is the competitor of the Western Union and both work same way. ... Another feaure that seperates Western Union from EFT system is if the ...
| PowerPoint PPT presentation | free to view
Title: PowerPoint Presentation Last modified by: Prof. Mostafa Created Date: 1/1/1601 12:00:00 AM Document presentation format:
| PowerPoint PPT presentation | free to download
Common forms of active attacks may ... indiscriminately With careful consideration when designing and developing network ... directory system, which ...
| PowerPoint PPT presentation | free to view
The broadcast nature of the channel makes it easier to be tapped ... and authenticates sender; guards against message modification and impersonation ...
| PowerPoint PPT presentation | free to download
Chapter 8: Scrambling Through Cryptography Security+ Guide to Network Security Fundamentals Second Edition Objectives Define cryptography Secure with cryptography ...
| PowerPoint PPT presentation | free to download
Objectives Define cryptography Secure with cryptography hashing algorithms Protect with symmetric encryption algorithms Harden with asymmetric encryption algorithms ...
| PowerPoint PPT presentation | free to view
Nokia develop Smart Messaging, Timetabling Markup Language (TTML) 1997 ... WAP-210, Wireless Application Protocol Architecture Specification ...
| PowerPoint PPT presentation | free to download
S-BGP sequence of messages sigs. 4096 byte size limit (M1, ... PKi = e(g,g)ai ,hi=gyi', ui,1=gyi,1...,um, =gyi,m. SK =ai ,yi', yi,1,...,yi,m. Agg(SKi,Mi, ...
| PowerPoint PPT presentation | free to download
Key usage settings SHALL be set in accordance with RFC 3280 definitions. Further conventions for key usage setting MAY be defined by certificate policies ...
| PowerPoint PPT presentation | free to download
Patterns Arquitet nicos para E-Business Acervo de patterns arquitet nicos nivelados Favorecem aos arquitetos de sistemas implementar solu es de e-business de ...
| PowerPoint PPT presentation | free to download
... Normal patient that accepts exchange of patient information Patient asks for accounting of ... Health Information Exchange (HIE) International ...
| PowerPoint PPT presentation | free to download
Security is only about protecting 'things' We don't have any information anyone would want ... Our people won't tolerate tight security. My PC is secure, so ...
| PowerPoint PPT presentation | free to download
Signing algo. S(may be probabilistic): input: message m, (Kp, Ks) output: signature s. Verification algo. V (not probabilistic): input: m, Kp, s. output: accept or ...
| PowerPoint PPT presentation | free to download
Differentiate between two categories of cryptography schemes ... Know how and where IPSec, TLS, and PPG provide security. Objectives. TCP/IP Protocol Suite ...
| PowerPoint PPT presentation | free to view
Signature data tag to ensure. a) Source b) Integrity c) anti-forgery. Access Control ... Gatekeeper: password-based login, screening logic ...
| PowerPoint PPT presentation | free to download
Assures that a communication is authentic. Assures the recipient that the message is from ... Encipherment, digital signatures, access controls, data integrity, ...
| PowerPoint PPT presentation | free to view
Figure 1: SDR / MExE Download Framework Repository (Java sandbox) Download + Verification Using MExE Network MExE MExE Applet SDR Forum Manufacturer Header:
| PowerPoint PPT presentation | free to download
Dr. Robert J. Boncella. Washburn University. 2. Overview of Presentation ... Ford, W., Hallam-Baker, P., Fox, B., Dillaway, B., LaMacchia, B., Epstein, J. ...
| PowerPoint PPT presentation | free to download
Title: Detecting Hijacked Prefixes? Author: Geoff Huston Last modified by: gih Created Date: 4/27/2005 12:40:56 AM Document presentation format: On-screen Show
| PowerPoint PPT presentation | free to download
Operations vary for every company. Hardware, communications lines and ... how to respond to a security incident be it a computer worm, mistake, hacker or ...
| PowerPoint PPT presentation | free to download
Border directory concept; 'White Pages' Use ACES for public transactions ... Ultimate bridge to CAs external to Federal government ...
| PowerPoint PPT presentation | free to view
Security and Cryptography Security: all issues which make secure communication (information transmission, two (multiple) party interaction) over insecure channels.
| PowerPoint PPT presentation | free to view
Title: Financial Reporting: The Institutional Setting Author: me Last modified by: chand Created Date: 9/14/2004 5:47:48 PM Document presentation format
| PowerPoint PPT presentation | free to download
VIRUS ... VIRUS CHARACTERISTICS. Fast. Easily invade and infect computer ... Update the latest antivirus software periodically. 22. WWW. Awad ...
| PowerPoint PPT presentation | free to view
free 30-day trial version. GnuPG is a freeware ... Thawte (21 day free trial) ... free personal use, but businesses receiving payments are charged a fee ...
| PowerPoint PPT presentation | free to view
http://ee.sharif.edu/~farhat. 2. ????? ?????? ??? ????????. ??? ?????. ??????? ???? ??? ??????? ... ????? ?? ?? ????? ???? ??? ???????. ????? ?????? ??? ?? ...
| PowerPoint PPT presentation | free to view
Created Date: 1/1/1601 12:00:00 AM Document presentation format: On-screen Show (4:3) Other titles: Arial Times New Roman Default Design 1_Default Design 2_Default ...
| PowerPoint PPT presentation | free to view
Confidentiality, Privacy and Security Privacy The desire of a person to control the disclosure of personal health information Confidentiality The ability of a person ...
| PowerPoint PPT presentation | free to download
Read client certificate : X509 URL read. Verify server certificate : WTLSCert ... Perform, Change, Block/Unblock, Enable/Disable. 24. 5/30/09 ...
| PowerPoint PPT presentation | free to download
Man-in-the-Middle Attack A man-in-the-middle attack is designed to intercept the transmission of a public key or even to insert a known key structure in place of the ...
| PowerPoint PPT presentation | free to download
Lycos business, career, or computer sections: $35/1000. Lycos mortgage-rate ... Lycos Inc. Post in all categories that fit and on industry-appropriate forums ...
| PowerPoint PPT presentation | free to download