Which of the following is not included in a firm PowerPoint PPT Presentation
1 / 100
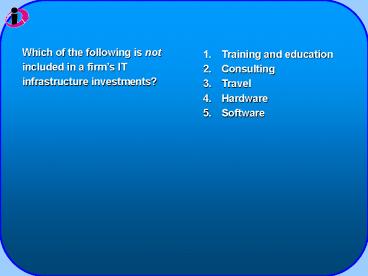
Title: Which of the following is not included in a firm
1
Which of the following is not included in a
firms IT infrastructure investments?
- Training and education
- Consulting
- Travel
- Hardware
- Software
2
The services a firm is capable of providing to
its customers, suppliers, and employees are a
direct function of the
- firms strategic 5-year plan.
- amount of money spent on hardware.
- amount of money spent on software.
- firms IT infrastructure.
- Not sure
3
Which of the following services provides
enterprise-wide capabilities that are shared by
all business units?
- Telecommunications
- Data Management
- Application software
- Physical facilities management
- IT education
4
Which of the following services focuses on video
connectivity for employees, customers, and
suppliers?
- Telecommunications
- Data Management
- Application software
- Physical facilities management
- IT education
5
- Physical facilities management
- Data management
- IT management
- IT education
- IT research and development
Which of the following services offers managers
training in how to plan for and manage IT
investments?
6
- Wintel
- Multitiered
- Simple
- Application
- Not sure
Which of the following defines the type of
client/server network in which several different
levels of servers are used?
7
Using individual atoms and molecules to create
computer chips and other devices is called
- atomic technology.
- nanotechnology.
- molecular engineering.
- Moores Law.
- transistor technology.
8
Which of the following is related to the idea
that the value of a network grows exponentially
as a function of the number of network members?
- Moores Law
- Microprocessor Power Law
- Law of Mass Digital Storage
- Metcalfes Law
- Not sure
9
- technology standards.
- network economics.
- product specifications.
- network specifications.
- Not sure
Specifications that establish the compatibility
of products is called
10
Ultrathin computers stored in racks popular in
the server market are called
- ultrathin computers.
- rack computers.
- blade servers.
- mainframes.
- Not sure
11
The most popular open-source operating system is
- Windows.
- Linux.
- Star Office.
- MAC OS 10.
- PeopleSoft.
12
- Storage area network
- Peoplesoft
- Web hosting services
- Microsoft
- RedHat
Which of the following provides fee-paying
subscribers with space to maintain their Web
sites?
13
- agility.
- self-healing computing.
- cost savings.
- speed of computation.
- Not sure
The business case for using grid computing
involves all of the following except
14
- Grid computing
- Autonomic computing
- On-demand computing
- Edge computing
- Open-source computing
Which of the following refers to firms
off-loading peak demand for computing power to
remote, large-scale data processing centers?
15
- Linux.
- Star Office.
- XML.
- HTML.
- Java.
An operating-system-independent,
processor-independent, object-oriented
programming language used on the Web is
16
- Middleware.
- XML.
- HTML.
- EAI software.
- Java.
The foundation technology for Web services is
17
A business that delivers and manages applications
and computer services from remote computer
centers is known as a(n)
- software outsourcer.
- utility computing provider.
- Internet service provider.
- edge computing provider.
- application service provider.
18
- Making wise infrastructure investments
- Allocating costs among business units
- Choosing IT components
- Dealing with change
- Determining market demands
Which of the following is not a challenge for
creating and managing a coherent IT
infrastructure?
19
- Market demand for your firms services
- Competitor firms IT investments
- Competitor firms IT services
- Your firms IT strategy
- Your firms business strategy
Which of the following factors in the competitive
forces model dictates that the firm make an
inventory of existing IT infrastructure costs?
20
- Travel to and from work
- Hardware acquisition
- Downtime
- Space and energy
- Training
Which of the following is not a component of the
Total Cost of Ownership of a firms IT
infrastructure?
21
When working with a database, a group of related
fields comprises a(n)
- file.
- database.
- entity.
- record.
- attribute.
22
A person, place, thing, or event on which we
store and maintain information using records is
a(n)
- file.
- database.
- entity.
- field.
- attribute.
23
A field in each record that uniquely identifies
that record is called a
- secondary field.
- primary field.
- key field.
- first field.
- customer field.
24
Which of the following is not a problem with the
traditional file environment?
- Data security
- Program-data dependence
- Data redundancy
- Easily sharing data
- Inflexibility
25
- Program-data dependence
- Data redundancy
- Inflexible database retrieval
- Lack of data sharing
- Data inconsistency
Which of the following occurs when the same data
are stored in more than one place or location?
26
- Program-data dependence
- Data redundancy
- Inflexible database retrieval
- Lack of data sharing
- Data inconsistency
Which of the following refers to the situation in
which a change in a software program could
require a change in the data used by that
program?
27
The software that acts as an interface between
application programs and the physical data files
is
- middleware.
- shareware.
- enterprise application software.
- database management system.
- operating system.
28
Which of the following refers to the presentation
of data as they would be perceived by end users?
- Conceptual schema
- Logical view
- Physical view
- Physical schema
- Subschema
29
- conceptual schema.
- logical view.
- physical view.
- physical schema.
- subschema.
The logical description of the entire database
showing all the data elements and relationships
among them is called the
30
Which of the following is not a component of a
database management system?
- Enterprise applications
- Data definition language
- Data manipulation language
- Data dictionary
- Not sure
31
An automated file that stores definitions of data
elements and data characteristics is called a(n)
- data definition language.
- data manipulation language.
- data dictionary.
- application program.
- Not sure
32
- Hierarchical
- Table
- Network
- Relational
- Not sure
Which type of data model represents all data in
the database as simple two-dimensional tables?
33
- Select
- Join
- Project
- Not sure
Which of the following is not a basic operation
in a relational database?
34
- Small
- Stable
- Flexible
- Adaptive
- Networked
Which of the following is not a characteristic of
data structures that have been normalized?
35
- mine.
- warehouse.
- store.
- network.
- crate.
A database that stores current and historical
data of potential interest to managers throughout
the company is called a data
36
- Data mining
- Data warehousing
- Data storing
- Data networking
- Data crating
Which of the following is often used to provide
information for targeted marketing campaigns?
37
Which of the following allows users to access
topics on a Web site in whichever order they wish?
- Structured Query Languages
- Hypermedia databases
- Ad-hoc query languages
- Common gateway interface
- Database servers
38
- SQL script.
- Data language script.
- Java script.
- Access script.
- Common gateway interface.
A specification for transferring information
between a Web server and a program designed to
accept and return data is called
39
- resource administration.
- data administration.
- database administration.
- Data-mining administration.
- Not sure
An organizational function with the power to
define information requirements for the entire
company is called a
40
- resources administration.
- data administration.
- database administration.
- data-mining administration.
- Not sure
A database design and management group performs
the functions of
41
In many companies, disparate networks are moving
toward a single common foundation based on
- enterprise applications.
- Internet technologies.
- intranet technologies.
- Windows operating systems.
- Linux operating systems.
42
Which of the following communication trends has
created many alternatives for local phone service?
- Rapid technological innovation
- Rapid growth in wireless technologies
- Rapid growth in broadband connections
- Telecommunications deregulation
- Not sure
43
According to Metcalfes Law, the more people
participating in a network, the
- more work will be done.
- less work will be done.
- greater its value.
- the less its value.
- Not sure
44
Which of the following is not a business value
impact of the telecommunications revolution?
- Improved temporal barriers
- Higher quality decisions
- Declining agency costs
- Increased agility
- Declining geographical barriers
45
- computer network interface.
- computer interface device.
- broadband connection.
- high-speed interface card.
- network interface card.
Each computer on a network contains a network
interface device called a
46
- hub.
- switch.
- router.
- network operating system.
- protocol.
A special communications processor used to route
packets of data through different networks is a
47
A method of slicing digital messages into parcels
and then sending them through a network using
different paths is called
- parcel slicing.
- parcel switching.
- packet switching.
- packet slicing.
- packet routing.
48
Corporate networks are using a single, common,
worldwide standard known as
- NIC.
- TCP/IP.
- OSI.
- DWDM.
- Wi-Fi.
49
- Application layer
- Transport layer
- Internet layer
- Operating system layer
- Network layer
Which of the following is not one of the four
layers of the TCP/IP reference model for
communications?
50
A set of rules and procedures governing
transmission of information between two points in
a network is called
- switches.
- open systems model.
- dense wavelength division multiplexing.
- protocols.
- Not sure
51
The physical transmission media type that
consists of thickly insulated and shielded copper
wire is
- fiber-optic cable.
- coaxial cable.
- twisted wire.
- optical broadband.
- microwave cable.
52
- Cable modems
- Digital subscriber lines
- Microwaves
- T-1 lines
- Not sure
Which of the following operates over existing
copper telephone lines to carry voice, data, and
video?
53
- IP address.
- TCP address.
- OSI address.
- DSL address.
- Not sure
Every computer on the Internet is assigned a
unique
54
- Network operating system
- TCP/IP
- Internet governance system
- Domain name system
- Internet service system
Which system converts IP addresses to domain
names?
55
- Telnet
- File Transfer Protocol
- World Wide Web
- Usenet newsgroups
- Infodata transfer
Which of the following is not an Internet service
to which a client computer has access?
56
- Ubiquity
- Richness
- Hardware platform
- Customization
- Information density
Which of the following is not a unique feature of
Internet technology?
57
The communications standard used to transfer
pages on the Web is
- XML.
- HTML.
- HTPM.
- HTTP.
- FTP.
58
- Enterprise software
- Search engine
- FTP
- Web servers
- Telnet
Which of the following contains software that
looks for Web pages containing one or more search
terms?
59
- Overture.
- AOL.
- Google.
- Yahoo.
- Altavista.
The most popular Web search tool is
60
- Telnet
- VoIP
- FTP
- HTTP
- VPN
Which of the following uses the Internet Protocol
to deliver voice information in digital form?
61
Which of the following is not a business value
that companies can realize from the increased use
of wireless networking?
- More flexible work arrangements
- Save on wiring offices
- Makes moving employees easier
- Increases worker productivity
- Fewer software programs
62
Which of the following combine wireless
communication with tracking capabilities from GPS
systems?
- Microwave systems
- Satellite positioning systems
- Telematics
- VHF-TV
- Not sure
63
Which systems transmit high-frequency radio
signals through the atmosphere and are widely
used for high-volume, point-to-point
communications?
- Microwave systems
- Infrared systems
- Paging systems
- Satellite systems
- Cell phone systems
64
A system of protocols and technologies that
enables cell phones and other wireless devices to
access Web-based information and services is
called
- wireless markup language.
- wireless application protocols.
- microbrowser.
- I-mode.
- Not sure
65
- wireless markup language.
- wireless application protocol.
- microbrowser.
- I-mode.
- Not sure
To access Web-based information, a person with a
WAP-compliant phone would use a(n)
66
- Wi-fi.
- Wi-max.
- Wi-mod.
- Bluetooth.
- Wireless NIC.
The 802.15 wireless networking standard useful
for creating small personal area networks is
known as
67
A box consisting of a radio receiver/transmitter
and antennas that link to a wired network,
router, or hub is called a(n)
- access point.
- wireless NIC.
- LAN bridge.
- antenna point.
- Wi-Max.
68
One or more access points positioned in strategic
public places to provide maximum wireless
coverage are called
- EV-DO connections.
- DSL access points.
- cell access points.
- hotspots.
- Not sure
69
- too few users.
- too many users.
- weak security.
- difficulty in establishing a connection.
- Not sure
A major drawback of increased Wi-Fi usage is
70
Which of the following offers wireless access
ranges of up to 31 miles?
- Wi-Fi
- Wi-Max
- Bluetooth
- EV-DO
- GSM cellular service
71
A type of wireless computing, in which users move
from wireless hotspot to wireless hotspot, is
sometimes referred to as
- wardriving.
- nomadic computing.
- hotspot computing.
- hotspot jumping.
- access computing.
72
- wireless portals.
- sub-Web portals.
- nomadic portals.
- mobile portals.
- Not sure
Special Web sites that feature optimized content
and services for mobile devices are known as
73
- d-wallets.
- m-wallets.
- c-wallets.
- w-wallets.
- p-wallets.
Digital wallets used for wireless mobile commerce
transactions are referred to as
74
- cell phone transponders.
- pervasive computing.
- wireless sensor networks.
- RFID.
- bar codes.
A powerful technology for tracking the movement
of goods throughout a supply chain using tags
with embedded microchips is
75
- processor.
- antenna.
- hard drive.
- DVD recorder.
- motherboard.
RFID tags consist of a microchip that stores data
and a(n)
76
- Read/Write
- Active
- Passive
- RR/RW
- Not sure
Which of the following describes the type of RFID
tag that typically enables data to be rewritten
or modified?
77
The idea that computers will become increasingly
embedded in our natural movements and throughout
our environment is referred to as
- environmental computing.
- wireless computing.
- nomadic computing.
- pervasive computing.
- Not sure
78
- ZigBee protocols
- IP protocols
- TCP protocols
- Environmental protocols
- Not sure
Which of the following is widely used in wireless
sensor networks that control environmental
factors such as heating, air conditioning, and
lighting in buildings?
79
- Managing the technology
- Integrating the technology into the IT
infrastructure - Determining the appropriate number of users
- Maintaining security
- Maintaining privacy
Which of the following is not necessarily a
management challenge posed by wireless technology?
80
- Determine the validity of wireless computing
- Identify areas in which it can provide value
- Create a framework for the technology
- Use pilot programs to test wireless systems
- Not sure
Which of the following is not a guideline for
managing mobile technology in the enterprise?
81
Which of the following is not a source of common
threats against contemporary information systems?
- Too many users
- Technical factors
- Organizational factors
- Environmental factors
- Poor management decisions
82
The act of eavesdroppers driving by buildings or
parking outside and intercepting wireless network
traffic is called
- eavesdropping.
- war driving.
- driving interception.
- wireless interception.
- Not sure
83
Computer viruses, worms, and Trojan horses are
collectively called
- spyware.
- spam.
- groupware.
- malware.
- macroware.
84
A rogue software program that attaches itself to
other software programs or data files in order to
be executed is called a
- Trojan horse.
- worm.
- virus.
- spoofer.
- spammer.
85
- Trojan horse.
- worm.
- virus.
- spoofer.
- spammer.
A software program that appears to be benign, but
then does something other than expected is called
a
86
- Trojan horse
- worm.
- virus.
- spoofer.
- spammer.
An independent computer program that copies
itself from one computer to others over a network
and operates on its own is referred to as a
87
A type of eavesdropping program that monitors
information traveling over a network is known as
- a spoofer.
- a sniffer.
- spyware.
- spam.
- spybot.
88
A crime in which an imposter obtains key pieces
of personal information in order to impersonate
another person is known as
- spoofing.
- identity theft.
- denial of service attack.
- fraud.
- breach of confidentiality.
89
- phishing.
- faking.
- spotting.
- denial of service.
- theft.
The act of setting up fake Web sites or sending
emails that look like those of legitimate
businesses asking users for confidential personal
data is called
90
The largest financial threats to business
institutions come from
- the competition.
- customers.
- suppliers.
- the government.
- insiders.
91
A major source of errors introduced into an
information system comes from
- suppliers.
- customers.
- business partners.
- employees.
- networks.
92
- customer input.
- supplier access.
- presence of hidden bugs.
- network access points.
- business partner input.
A major problem with software is
93
- HIPAA
- Gramm-Leach-Bliley Act
- Sarbanes-Oxley Act of 2002
- ISO 17799
- Child Decency Act
Which of the following pieces of government
legislation was designed to protect investors
from financial scandals?
94
- general controls.
- input controls.
- processing controls.
- output controls.
- network controls.
The type of control associated with the accuracy
and completeness of data when they enter the
system is referred to as
95
- Value of information assets
- Points of vulnerability
- Likely frequency of a problem
- Potential for damage
- Cost of erroneous data
Which of the following is not an element of a
risk assessment?
96
- Ranking information risks
- Identifying acceptable security goals
- Level of acceptable risk
- Number of network access points
- Identifying security goals
Which of the following is not an integral part of
a well-formulated security policy?
97
Which of the following is not a method of
ensuring business continuity associated with
information systems?
- Fault-tolerant systems
- High-availability systems
- Limiting the number of users
- Load balancing
- Mirroring
98
- Access control
- Authentication
- Biometric authentication
- Firewalls
- Spyware
Which of the following consists of all the
policies and procedures a company uses to prevent
improper system access by unauthorized outsiders?
99
- Intrusion Detection systems
- Authentication
- Biometric authentication
- Firewalls
- Spyware
Which of the following access controls is based
on the measurement of a physical or behavioral
trait that makes each individual unique?
100
- secure sockets layer.
- public key infrastructure.
- secure hypertext transfer protocol.
- transport layer security.
- digital certificates.
A method for encrypting data flowing over the
Internet, but limited to Web documents is