Token-passing Algorithms PowerPoint PPT Presentation
Title: Token-passing Algorithms
1
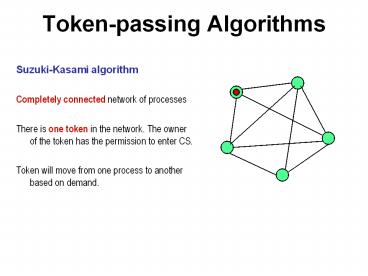
Token-passing Algorithms
- Suzuki-Kasami algorithm
- Completely connected network of processes
- There is one token in the network. The owner of
the token has the permission to enter CS. - Token will move from one process to another based
on demand.
2
Suzuki-Kasami Algorithm
- Process i broadcasts (i, num)
- Each process maintains
- -an array req reqj denotes the sequence no of
the latest request from process j - (Some requests will be stale soon)
- Additionally, the holder of the token maintains
- -an array last lastj denotes the sequence
number of the latest visit to CS from for process
j. - - a queue Q of waiting processes
Q
Sequence number of the request
req array0..n-1 of integer
last array 0..n-1 of integer
3
Suzuki-Kasami Algorithm
- When a process i receives a request (i, num) from
- process k, it sets reqk to max(reqk, num)
- and enqueues the request in its Q
- When process i sends a token to the head of Q,
- it sets lasti its own num, and passes the
array - last, as well as the tail of Q,
- The holder of the token retains process k in its
- Q only if 1 lastk reqk
- This guarantees the freshness of the request
Req array0..n-1 of integer
Last Array 0..n-1 of integer
4
Suzuki-Kasamis algorithm
- Program of process j
- Initially, ?i reqi lasti 0
- Entry protocol
- reqj reqj 1
- Send (j, reqj) to all
- Wait until token (Q, last) arrives
- Critical Section
- Exit protocol
- lastj reqj
- ?k ? j k ? Q ? reqk lastk 1 ? append k
to Q - if Q is not empty ? end (tail-of-Q, last) to
head-of-Q fi - Upon receiving a request (k, num)
- reqk max(reqk, num)
5
Example
req1,0,0,0,0
req1,0,0,0,0 last0,0,0,0,0
1
0
2
req1,0,0,0,0
4
req1,0,0,0,0
3
req1,0,0,0,0
initial state
6
Example
req1,1,1,0,0
req1,1,1,0,0 last0,0,0,0,0
1
0
2
req1,1,1,0,0
4
req1,1,1,0,0
3
req1,1,1,0,0
1 2 send requests
7
Example
req1,1,1,0,0
req1,1,1,0,0 last1,0,0,0,0 Q(1,2)
1
0
2
req1,1,1,0,0
4
req1,1,1,0,0
3
req1,1,1,0,0
0 prepares to exit CS
8
Example
req1,1,1,0,0 last1,0,0,0,0 Q(2)
req1,1,1,0,0
1
0
2
req1,1,1,0,0
4
req1,1,1,0,0
3
req1,1,1,0,0
0 passes token (Q and last) to 1
9
Example
req2,1,1,1,0 last1,0,0,0,0 Q(2,0,3)
req2,1,1,1,0
1
0
2
req2,1,1,1,0
4
req2,1,1,1,0
3
req2,1,1,1,0
0 and 3 send requests
10
Example
req2,1,1,1,0
req2,1,1,1,0
1
0
2
req2,1,1,1,0 last1,1,0,0,0 Q(0,3)
4
req2,1,1,1,0
3
req2,1,1,1,0
1 sends token to 2
11
Raymonds tree-based algorithm
1
4
1
4,7
1,4
1,4,7 want to enter their CS
12
Raymonds Algorithm
1
4
1,4
4,7
2 sends the token to 6
13
Raymonds Algorithm
4
4
4
4,7
6 forwards the token to 1
The message complexity is O(diameter) of the
tree. Extensive Empirical measurements show that
the average diameter of randomly chosen trees of
size n is O(log n). Therefore, the authors claim
the average message complexity to be O(log n)
14
Distributed snapshot
- -- How many messages are in transit
- on the internet?
- -- What is the global state of a distributed
system of N processes? - How do we compute these?
15
One-dollar bank
Let a 1 coin circulate in a network of a million
banks. How can someone count the total in
circulation? If not counted properly, then one
may think the total in circulation to be one
million.
16
Importance of snapshots
- Major uses in
- - deadlock detection
- - termination detection
- - rollback recovery
- - global predicate computation
17
Consistent cut
A cut is a set of events.
- (a ? consistent cut C) ? (b happened before
a) ? b ? C
b
g
c
a
d
P1
e
m
f
P2
P3
k
h
i
j
Cut 1
Cut 2
(Not consistent)
(Consistent)
18
Consistent snapshot
- The set of states immediately following a
consistent cut forms a consistent snapshot of a
distributed system. - A snapshot that is of practical interest is the
most recent one. Let C1 and C2 be two consistent
cuts and C1 ? C2. Then C2 is more recent than C1. - Analyze why certain cuts in the one-dollar bank
are inconsistent.
19
Consistent snapshot
- How to record a consistent snapshot? Note that
- 1. The recording must be non-invasive
- 2. Recording must be done on-the-fly.
- You cannot stop the system.
20
Chandy-Lamport Algorithm
- Works on a
- (1) strongly connected graph
- (2) each channel is FIFO.
- An initiator initiates the algorithm by sending
out a marker ( )
21
White and red processes
- Initially every process is white. When a process
receives a marker, it turns red if it has not
already done so. - Every action by a process, and every message sent
by a process gets the color of that process.
22
Two steps
- Step 1. In one atomic action, the initiator (a)
Turns red (b) Records its own state (c) sends a
marker along all outgoing channels - Step 2. Every other process, upon receiving a
marker for the first time (and before doing
anything else) (a) Turns red (b) Records its own
state (c) sends markers along all outgoing
channels - The algorithm terminates when (1) every process
turns red, and (2) Every process has received a
marker through each incoming channel.
23
Why does it work?
- Lemma 1. No red message is received in a white
action.
24
Why does it work?
All white
All red
SSS
Easy conceptualization of the snapshot state
- Theorem. The global state recorded by
Chandy-Lamport algorithm is equivalent to the
ideal snapshot state SSS. - Hint. A pair of actions (a, b) can be scheduled
in any order, if there is no causal order between
them, so (a b) is equivalent to (b a)
25
Why does it work?
Let an observer observe the following
actions wi wk rk wj ri wl rj rl
? wi wk wj rk ri wl rj rl
Lemma 1 ? wi wk wj rk wl ri rj
rl Lemma 1 ? wi wk wj wl rk ri
rj rl done!
Recorded state
26
Example 1. Count the tokens
- Let us verify that Chandy-Lamport snapshot
algorithm correctly counts - the tokens circulating in the system
D
C
A
B
How to account for the channel states? Use sent
and received variables for each process.