Flow of ISMS endeavors based on the PDCA cycle PowerPoint PPT Presentation
1 / 1
Title: Flow of ISMS endeavors based on the PDCA cycle
1
Materials 3
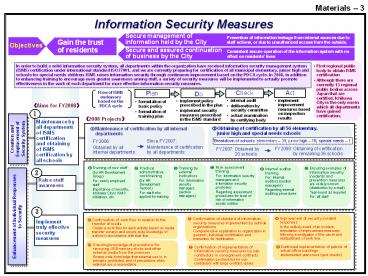
Information Security Measures
Prevention of information leakage from internal
sources due to staff actions, or due to
unauthorized access from the outside.
Consistent secure operation of the information
system with no effect on residents lives
In order to build a solid information security
system, all departments within the organization
have received information security management
system (ISMS) certification under international
standard ISO27001, and we are currently preparing
for certification of all municipal elementary,
junior high and schools for special needs
children. ISMS raises information security
through continuous improvement based on the PDCA
cycle. In 2008, in addition to enhancing training
to encourage even greater awareness among staff,
a variety of security measures will be
implemented to actually promote effectiveness in
the work of each department for more effective
information security measures.
First regional public body to obtain ISMS
certification Although there are currently 13
regional public bodies across Japan that are
certified, Ichikawa City is the only one in which
all departments have gained certification.
Do
Check
Act
Plan
Flow of ISMS endeavors based on the PDCA cycle
internal audit deliberation by security
committee actual examination by certifying body
implement improvement measures based on
inspection results
implement policy prescribed in the plan
implement security measures prescribed in the
ISMS standard
formulation of basic policy formulation of
training plan
Aims for FY2008
1
2008 Projects
Maintenance by all departments of ISMS
certification and obtaining of ISMS certification
by all schools
? Obtaining of certification by all 56
elementary, junior high and special needs schools
? Maintenance of certification by all internal
departments
Creation and Emplacement of Security System
Breakdown of schools elementary 39 junior
high 16 special needs 1
Since FY2007 Maintenance of certification by
all departments
FY2006 Obtained by all internal departments
FY2008 Obtaining of certification by remaining
36 schools
FY2007 Obtained by 20 schools
? Risk assessment training For Information
security managers and information security
promoters Regarding assessment procedures for
level of risk of information assets outflow
? Ensuring examples of information security
incidents and prevention measures are widely
known (distribution by e-mail) Year-round as
required For all staff
? Training of new staff (by HR Development
Group) For newly employed staff Importance of
security, Ichikawa Citys ISMS initiatives, etc.
? Practical administrative work training (by HR
Development Section) For staff who applied for
training
? Training by external instructors For
Information security managers (section managers)
? Internal auditor training For Internal
auditors (section managers) Regarding internal
auditing procedures
2
Raise staff awareness
3
Enhancement of Individual Responses to Security
? Improvement of security incident responses In
the unlikely event of an incident, formulation of
improvement measures following investigation of
the cause and readjustment of work flow.
? Confirmation of standard of information
security measures implemented by outside
organizations Comprehensive explanation to
organization in question, individual confirmation
and instruction for rectification
Implement truly effective security measures
? Confirmation of work flow in relation to the
transfer of media Create a work flow for each
activity based on media transfer surveys and
ensure wide knowledge of actions in accordance
with that flow.
? Ensuring knowledge of precautions for removing
USB memory sticks and other external media from
the premises Ensure wide knowledge that external
use is, in principle, prohibited, and of
precautions when external use is unavoidable
? Continued implementation of patrols of actual
office buildings Implemented year-round (spot
checks)
? Confirmation of implementation of information
security measures by sub-contractors in
consignment contracts Confirmation by check list
for sub-contractors with large contract values