Lawful Interception System PowerPoint PPT Presentations
All Time
Recommended
... Solution Concept The Probe is a software-based ... 100MCPS per channel ISDN Framing ... A-Interface input streams towards 2G/2.5G Radio ...
| PowerPoint PPT presentation | free to view
Global lawful interception market size is expected to reach $12.78 Bn by 2028 at a rate of 22.8%, segmented as by device, mediation devices, routers, intercept access point (iap), gateways, switches, management servers, others
| PowerPoint PPT presentation | free to download
Cyber threats are internet-based attempts aimed at disrupting or damaging IT systems of enterprises and hack critical information. Lawful interception refers to legally authorized surveillance of data and voice communication; it constitutes an important tool for law enforcement agencies worldwide for investigating and litigating criminal activities and tackle the ever-growing threat of terrorism. Lawful interception is applicable for all networks that deliver voice, data, and internet services. View more details of "Lawful Interception market" @ http://www.bigmarketresearch.com/global-lawful-interception-market
| PowerPoint PPT presentation | free to download
A Major Success. Started with 17th January 1995 Resolution 'Filled out' LEA requirements 1996 ... MF = Mediation function. NWO = Network operator. SvP = Service ...
| PowerPoint PPT presentation | free to view
The Global Lawful Interception Market is expected to reach $2,789.7 million by 2022, growing at 23.1% CAGR by 2022. Full report - https://kbvresearch.com/global-lawful-interception-market/
| PowerPoint PPT presentation | free to download
Title: Lawful Intercept Standardisation Requirements Author: BT GES Last modified by: Gulbani Giorgi Created Date: 10/19/2005 11:40:41 AM Document presentation format
| PowerPoint PPT presentation | free to download
Bharat Book Bureau provides the report, on “Global Lawful Interception Market 2016-2020” This report, Global Lawful Interception Market 2015-2019, has been prepared based on an in-depth market analysis with inputs from industry experts. https://www.bharatbook.com/information-technology-market-research-reports-643562/global-lawful-interception1.html
| PowerPoint PPT presentation | free to download
According to the latest research report by IMARC Group, The United States lawful interception market size reached US$ 1,134 Million in 2022. Looking forward, IMARC Group expects the market to reach US$ 2,148 Million by 2028, exhibiting a growth rate (CAGR) of 10.2% during 2023-2028. More Info:- https://www.imarcgroup.com/united-states-lawful-interception-market
| PowerPoint PPT presentation | free to download
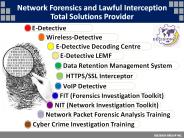
Network Forensics and Lawful Interception Total Solutions Provider DECISION GROUP INC. E-Detective Wireless-Detective E-Detective Decoding Centre E-Detective LEMF
| PowerPoint PPT presentation | free to download
interception: action (based on the law), performed by an network ... Encrypted IP Telephony (e.g. pgp -phone and Nautilus) etc. If applied by NWO/AP/SvP then ...
| PowerPoint PPT presentation | free to download
“Global Lawful Interception Market” report offers determining insights into the overall industry along with the market dimensions and assessment for the duration 2018 to 2025.
| PowerPoint PPT presentation | free to download
The All-in-One Mobile WLAN Interception System References ... Wireless-Detective Forbidder Mode WLAN Jammer/Forbidder Implementation in Wireless-Detective system: ...
| PowerPoint PPT presentation | free to download
Get a sample brochure @ http://tinyurl.com/z7g7k2y Lawful Interception (LI) is a security process in which a service provider or network operator collects and provides intercepted communications of individuals or organizations to law enforcement agencies. LI is used by law enforcement agencies (LEAs), regulatory or administrative agencies, and intelligence services to prevent crime, including fraud and terrorism. Recent developments in data-based communications have unveiled new channels for lawful interception. The expansion in networks and increased telecommunication activities promote lawful interception activities.
| PowerPoint PPT presentation | free to download
The global lawful interception market size is expected to grow from $2.96 billion in 2021 to $3.57 billion in 2022 at a compound annual growth rate (CAGR) of 20.64%.
| PowerPoint PPT presentation | free to download
Global Lawful Interception Market 2015-2019 has been prepared based on an in-depth market analysis with inputs from industry experts. It also covers the market landscape and lists growth prospects. The report includes a discussion of the key vendors operating in this market. Read Complete Report @ http://www.sandlerresearch.org/global-lawful-interception-market-2015-2019.html .
Lawful Interception / Data Retention. IPTV, RFID, safety services (emergency communications) ... FIGS (Fraud Information Gathering System) Terminate fraudulent ...
| PowerPoint PPT presentation | free to download
Partnerships, Programs and Practical Alternatives for System Transformation ... System 'cultures' appear to have divergent goals ...
| PowerPoint PPT presentation | free to view
car. car. car. The power law of settlements ... Quotes. Distributed. Cache. Web. Server. CORBA. RMI. XML-RPC. WebService. JMS. JDBC ...
| PowerPoint PPT presentation | free to view
CHAPTER 6 Linear Systems of Equations MULTIPLICATION AND ADDITION METHOD This method combines the multiplication property of equations with the addition/subtraction ...
| PowerPoint PPT presentation | free to download
Cross-Systems Mapping Transforming Services for Persons with Mental Illnesses and/or Substance Abuse Disorders in Contact with the Criminal Justice System
| PowerPoint PPT presentation | free to download
7 Chapter Securing Information Systems * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * * Establishing a Framework for Security and Control ...
| PowerPoint PPT presentation | free to view
Bus arbitration decides which device (bus master) gets the ... multiple devices may request (arbitrate for) the bus; fixed priority by address ...
| PowerPoint PPT presentation | free to download
... password to ... to-Peer (P2P) Sharing programs allow users to share files, ... In a hacking contest many users downloaded a 'hacking script' to attack ...
| PowerPoint PPT presentation | free to view
html head meta HTTP-EQUIV='content-type' CONTENT='text/html; charset=ISO-8859 ... HTTP learns the IP address of the web server, adds its header, and calls TCP. ...
| PowerPoint PPT presentation | free to view
Polar Coordinate System CALCULUS-III Dr. Farhana Shaheen Polar Coordinate System In mathematics, the polar coordinate system is a two-dimensional coordinate system in ...
| PowerPoint PPT presentation | free to download
Title: PowerPoint Presentation Author: KL Last modified by: user Created Date: 3/5/2005 9:57:46 AM Document presentation format: On-screen Show Company
| PowerPoint PPT presentation | free to download
Access only to files required for work. Read-only access. Certain time periods for ... Network scanners distinguish between real and fake APs. Netstumbler ...
| PowerPoint PPT presentation | free to view
... code runs in a restricted svchost instance) you need to be ... Control is never passed to the application for installation purposes (no setup.exe) ...
| PowerPoint PPT presentation | free to view
MEMBRANE PROTEINS ASSOCIATE WITH LIGANDS AT THE CELL SURFACE ... COPPER: ABSORBED IN THE JEJUNUM. ABOUT 50% OF THE INGESTED LOAD ABSORBED. ...
| PowerPoint PPT presentation | free to download
E-Detective HTTPS/SSL Interception MITM & Proxy Decision Group www.edecision4u.com Introduction to HTTPS/SSL Interception Intercept HTTPS/SSL traffic (connection ...
| PowerPoint PPT presentation | free to download
http://www.comstrac.com/ ......ComsTrac Limited specialises in providing professional surveillance and protection equipment for Law Enforcement Agencies, supplying all forms of communication intercept systems, for GSM, CDMA, Satellite, Computer and Standard Telephone Communications.
| PowerPoint PPT presentation | free to download
http://www.comstrac.com/ .ComsTrac Limited specialises in providing professional surveillance and protection equipment for Law Enforcement Agencies, supplying all forms of communication intercept systems, for GSM, CDMA, Satellite, Computer and Standard Telephone Communications.
| PowerPoint PPT presentation | free to download
Exploring the Solar System: all about spacecraft/spaceflight. How ... (tons of solar system debris --a ... to the outer Solar System (Jupiter or beyond) ...
| PowerPoint PPT presentation | free to view
3GPP SA3 Lawful Intercept Brye Bonner Chair SA3-LI 3GPP Organization Services Aspect (SA); Security (SA WG3); Lawful Intercept (SA WG3-LI) 3GPP Schedule for latest ...
| PowerPoint PPT presentation | free to download
Computer Systems and Security--- New era of secure communications ---Lecture 1 * Last lecture we saw the data encryption standard. However this require that the ...
| PowerPoint PPT presentation | free to view
(credibility,efficiency,solvency) Good's Quality & Quantity. After-sales assistance ... Buyer's Solvency. Business Risk Involved. 18. 10/6/09 ...
| PowerPoint PPT presentation | free to view
Rb = 1000 bits / sec. INFORMATION RATE vs. SYMBOL RATE (Cont. ... Rb = information rate = (1/T) Log2 M = 1/Tb. Where M = # of levels in the M-ary waveform ...
| PowerPoint PPT presentation | free to download
US has higher opportunity cost in making Nike shoes ... China will make Nike shoes and export to US. US will produce wheat and export to China ...
| PowerPoint PPT presentation | free to view
CSE2500. System Security and Privacy. CSE2500 System Security and Privacy Nandita&Srini ... Any added devices (such as alarms, bull terrier, etc...
| PowerPoint PPT presentation | free to view
ITU-T Workshop on Security - Seoul (Korea), 13-14 May 2002. Importance of Network Security ... Source: Information Week. CONCERNS OF I/T EXECUTIVES. 5. 9/4/09 ...
| PowerPoint PPT presentation | free to download
Title: Slide 1 Author: Stephanie Montgomery Last modified by: sbarclay Created Date: 2/27/2006 7:49:58 PM Document presentation format: On-screen Show
| PowerPoint PPT presentation | free to download
... systems boundaries have progressively become more 'porous,' especially in the Web environment. ... protocols allow users, designers, and evaluators of ...
| PowerPoint PPT presentation | free to download
(personal credit report) www.myidfix.com (identity theft repair) www.indentity_theft_fraud.org ... www.ftc.gov/bcp/conline/pubs/credit/idtheft.pdf ...
| PowerPoint PPT presentation | free to view
solution: homogeneous liquid or solid A-B phase ... (Stephen Hawking) 17. In terms of mole fractions instead of moles: - Divide (5) and (6) by nA nB: ...
| PowerPoint PPT presentation | free to view
Deep Space 2 (lost with Mars Polar Lander) But more to come in future: ... At what speeds are these things traveling through space? ...
| PowerPoint PPT presentation | free to download
Feasible Privacy for Lightweight RFID Systems. David Evans. work ... evans/talks/spar07. Photo by Bill Bryant. Protest at Texas Wal-Mart ... Duc, Park, Lee, ...
| PowerPoint PPT presentation | free to download
Temperature at a point Perturbation in PDF Generic definition: Change in output for an infinitesimal change ... Laboratory UNCERTAINTY ANALYSIS USING SSFEM ...
| PowerPoint PPT presentation | free to view
MA in Computer Science. 25 years software development. 15 ... Emulator 400 lines. 25 calls/sec. 250 concurrent calls. Start to first successful call: ~ 1 week ...
| PowerPoint PPT presentation | free to download
1. EOS 740 Hyperspectral Imaging Systems. February 25, 2005 Week 5. Ron Resmini ... Azimuth, relative/absolute. 11. Some Simplified RT Expressions ...
| PowerPoint PPT presentation | free to view
FOR MORE CLASSES VISIT www.law531mart.com LAW 531 Week 1 Practice Alternative Dispute Resolution LAW 531 Week 2 Practice Business Entities LAW 531 Week 3 Practice IRAC Review LAW 531 Week 4 Practice Intellectual Property
| PowerPoint PPT presentation | free to download
The research firm Contrive Datum Insights has just recently added to its database a report with the heading global Signal Intelligence Systems Market .Both primary and secondary research methodologies have been utilised in order to conduct an analysis of the worldwide Signal Intelligence Systems Market . In order to provide a comprehensive comprehension of the topic at hand, it has been summed up using appropriate and accurate market insights.
| PowerPoint PPT presentation | free to download
Debate. Divide into 2 groups - one group will be 'the government' and the other group ... You will debate the issues of encryption and interception of communications. ...
| PowerPoint PPT presentation | free to view
A parallelepiped is generated by the vectors. a , b and c. a. b. 4 ... Lattice points only at the corners of the parallelepiped. Lattice points at the corners ...
| PowerPoint PPT presentation | free to view
One of the most successful financial cybermediaries is PayPal. ... PayPal is accepted by thousands of businesses worldwide and is the preferred ...
| PowerPoint PPT presentation | free to view
... software or hardware tool to gain unauthorised ... Malware is a major problem. Encryption and authorisation technologies are major security techniques in use. ...
| PowerPoint PPT presentation | free to view
Started before the telephone was invented (using the telegraph) ... unfiltered traffic (meaning any other person's email who uses the same ISP) ...
| PowerPoint PPT presentation | free to view