Is Worms In Horses Dangerous PowerPoint PPT Presentations
All Time
Recommended
The worms cause lots of problems in horses like illness, dullness and listlessness. In worst case scenarios, it has been found that worms can even kill horses. There are different types of worms that have a greater impact on the health of your horse. Get best Pet Supplies at best price at VetSupply with free shipping.
| PowerPoint PPT presentation | free to download
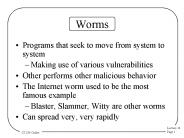
Worms Programs that seek to move from system to system Making use of various vulnerabilities Other performs other malicious behavior The Internet worm used to be the ...
| PowerPoint PPT presentation | free to download
Different viruses released with different malware intensions, out of which following are the 10 most dangerous viruses identified of all times
| PowerPoint PPT presentation | free to download
Spring 2006 CS 155 Network Worms: Attacks and Defenses John Mitchell with s borrowed from various (noted) sources Outline Worm propagation Worm examples ...
| PowerPoint PPT presentation | free to download
... a free service that allows you to create a temporary card number each time you ... CD-R / CD-RW. Another PC on a network. Create an emergency boot disk. ...
| PowerPoint PPT presentation | free to download
Anna Kournikova. Vulnerabilities. Computer hardware based on single trusted user ... Fake Viral signatures to protect against virus. Why should I care ? Reproduce ...
| PowerPoint PPT presentation | free to view
... and keep it in a safe place.Thanks Again and Have a ... Pranks. Vandalism. Attacking products of specific companies. To distribute political messages, ...
| PowerPoint PPT presentation | free to download
Virus/ Trojans/ Worms etc and some Common issues What is a Virus http://www.trendmicro.com/vinfo/virusencyclo/ What is a Worm? What is a virus hoax?
| PowerPoint PPT presentation | free to download
As an equestrian you will already be familiar with worms, however, guarding against worms is a tricky business as will become clear as you progress through our latest leaflet, read more... https://www.wormers.co.uk
| PowerPoint PPT presentation | free to download
"Virus, trojan horse and worms are dangerous threats having a knowledge about them helps you stay protected. An educated person can know if something goes wrong.
| PowerPoint PPT presentation | free to download
Virus, trojan horse and worms are dangerous threats having a knowledge about them helps you stay protected. An educated person can know if something goes wrong.
| PowerPoint PPT presentation | free to download
Malware is an abbreviation for ‘malicious software’. It is a software program or a script which is created with the intention of intruding and creating damage to computer systems. There are many types of malware namely bots, adware, worms, Trojan horses, spyware, virus, ransom ware and so on.
| PowerPoint PPT presentation | free to download
We will talk about. Computer worms, viruses, Trojan horses, and other programmed threats ... Click here to accept this worm:-- greeting cards ...
| PowerPoint PPT presentation | free to view
... common to horses. Identify different prevention methods for internal parasites in horses ... Most common in young horses. Tail rubbing is a common symptom ...
| PowerPoint PPT presentation | free to view
Anti-Tailgating Door. Shoulder Surfing. Most Dangerous Employees. Human ... Notice that the link is not only not PayPal, it is an IP address, 2 giveaways of ...
| PowerPoint PPT presentation | free to view
Essentially a combination of access control (firewall/router) and intrusion detection ... Worms, e.g. Blaster and MyDoom, that match a signature can be blocked. ...
| PowerPoint PPT presentation | free to download
Malware (Malicious Software) Viruses/Trojans/Worms. Spyware ... Code hidden inside another program. When program run, virus propagates (copies itself) to: ...
| PowerPoint PPT presentation | free to view
Virus Protection and Intrusion Detection John Mitchell Topics Trojans, worms, and viruses Virus protection Virus scanning methods Detecting system ...
| PowerPoint PPT presentation | free to download
Viruses and worms either standalone or carried by a program, document, or image ... Spybot Search & Destroy: http://security.kolla.de ...
| PowerPoint PPT presentation | free to view
Antivirus software. Detects viruses and worms. Electronic Commerce, Seventh Annual Edition ... site that offers free information about computer security ...
| PowerPoint PPT presentation | free to view
Worms travel in email self-contained. Common now. ... have reliable antivirus scanner running with up-to-date virus/worm definitions ...
| PowerPoint PPT presentation | free to view
Martin Luther Martin Luther was ... Charles V at the Diet of Worms in 1521 at which he was condemned. 1525 On the Bondage of the Will in answer to Erasmus ...
| PowerPoint PPT presentation | free to download
Implementing Distributed Internet Security using a Firewall Collaboration Framework ... Limit the impact of malware such as worms, viruses, and spam as well as the ...
| PowerPoint PPT presentation | free to view
Hacker**jhttp://www.kernelthread.com/mac/osx/tools_hacker.html ... Worms infiltrate computers usually by exploiting holes in the security of networked systems. ...
| PowerPoint PPT presentation | free to view
Computer Networking Part 2 Overview Virus s Worms Script kiddies Denial of Service Logic bombs Hackers Crackers Trojans Back doors Zombies Spam Hoaxes/chain letters ...
| PowerPoint PPT presentation | free to download
"The internet has revolutionized our lives in many positive ways, but just like a double edged sword, it has a dark side. Personal privacy can be compromised, leaving you, your company, and your clients at the hands of unscrupulous individuals. Personal files, bank account details, client information, and payment information can be hard to replace and potentially dangerous if it falls into the wrong hands. To mitigate against risks resulting from data leakage, it is of paramount importance to have a solid data security system. This is from an article that appeared on All Green Website: http://www.allgreenrecycling.com/blog/importance-data-security-electronics-2016/"
| PowerPoint PPT presentation | free to download
VetSupply is a leading online pet store with a comprehensive range of products that cater to all your pet needs. We strive to make pet treatments affordable and accessible to the most remote places of the country. Be it flea and tick preventatives, worming treatments, skin and coat supplies, dietary supplements or pet food, we have them all. Moreover, all our supplies come from renowned pharmacies like Bayer, Merial, MSD Animal Health, Zoetis, Royal Canin etc. and thus guarantee quality and efficiency.
Mcafee offers you the McAfee activate option to give best Home network protection, Multi-device protection, Web Protection, and Identity Theft.
| PowerPoint PPT presentation | free to download
Do you concern about the security of your online store? No worries, Read our blog to learn the about the security threats for eCommerce site & how to fix it.
| PowerPoint PPT presentation | free to download
Computer virus interferes with the working of the computer. It harms normal computer operation and can also harm the stored data in your computer. It can either corrupt the file or delete data permanently. But, computer experts can provide you help with Computer Virus Removal. You can contact Online Computer Repairservice providers to remove virus from your computer.
| PowerPoint PPT presentation | free to download
Computer virus interferes with the working of the computer. It harms normal computer operation and can also harm the stored data in your computer. It can either corrupt the file or delete data permanently. But, computer experts can provide you help with Computer Virus Removal. You can contact Online Computer Repairservice providers to remove virus from your computer.
| PowerPoint PPT presentation | free to download
MLS is the abridged type of McAfee LiveSafe, is one of the security arrangements created by the organization for keeping the clients' gadget and information protected and secure against the online dangers like Virus assaults, spyware, malware, and some more. In this manner, McAfee LiveSafe empowers the clients to proceed with their online exercises or remain associated with the computerized world over web, without getting contaminated by any infection assault.
| PowerPoint PPT presentation | free to download
McAfee is exceptional contrasted with other unmistakable affiliations that have been working for offering the best antivirus things to its clients so they may stay related with the pushed world by keeping up a key division from the dangers related with it. All the McAfee things give the layer of security to the clients' gadget (executing upon assortment stages like Android, Mac, iOS, and Windows) against the online dangers that may make hurt it in a few different ways
| PowerPoint PPT presentation | free to download
McAfee is one of the best eminent organizations that have been working for offering the best antivirus items to its clients so they may remain associated with the advanced world by maintaining a strategic distance from the dangers related with it. All the McAfee items give the layer of security to the clients' gadget (executing upon variation stages like Android, Mac, iOS, and Windows) against the online dangers that may make hurt it in a few different ways
| PowerPoint PPT presentation | free to download
Hardware based most routers (Linksys, D-Link, etc) also include a router ... Linksys' Instant Broadband EtherFast Cable/DSL Firewall Router with 4-Port ...
| PowerPoint PPT presentation | free to view
McAfee is one of the best eminent organizations that have been working for offering the best antivirus items to its clients so they may remain associated with the advanced world by keeping away from the dangers related with it. All the McAfee items give the layer of security to the clients' gadget (executing upon variation stages like Android, Mac, iOS, and Windows) against the online dangers that may make hurt it in a few different ways.
| PowerPoint PPT presentation | free to download
Malicious Software (Malware): Security tools and toolkits. Back doors (trap doors) Logic bombs ... Security Tools and toolkits. Automatically scan for computer ...
| PowerPoint PPT presentation | free to view
Presently a-days, the whole PC clients are very pulled in towards the web world and in this manner, because of this expanded web utilization the level of getting assaulted by some online dangers have been expanded substantially higher. In this manner, to keep the clients' gadget sheltered and secure from turning into a casualty of such online dangers or some phishing assault, many organization programming organization like McAfee has propelled its online security arrangements.
| PowerPoint PPT presentation | free to download
Title: PowerPoint Presentation - I. Introduction to class Author: Multimedia Development Lab Last modified by: Enotomology Created Date: 6/17/1995 11:31:02 PM
| PowerPoint PPT presentation | free to download
Analysis of Instant Messenger Programs. Celia Hung and Nathan Miller. ECE 478/578 ... The Problem with Instant Messaging Apps at Work.' www.cnet.com. August 2002 ...
| PowerPoint PPT presentation | free to view
In this era of modern technology, computers play a very important role in our daily lives. Computers play its functions in private homes, offices, workspaces, hospitals, schools, and everywhere else. It is undeniable that computers are very important nowadays but of course, no matter how great the technology is, there will st ill be some flaws and problems. The existence of computer viruses revolutionized the way the computer works and what type of security measures are supposed to be taken to prevent this serious problem. more info http://activatesoft.blogspot.com
| PowerPoint PPT presentation | free to download
Security Tools and toolkits. Automatically scan for ... that install them or may contain booby-trap that will compromise the systems that install them. ...
| PowerPoint PPT presentation | free to view
In this era of modern technology, computers play a very important role in our daily lives. Computers play its functions in private homes, offices, workspaces, hospitals, schools, and everywhere else. It is undeniable that computers are very important nowadays but of course, no matter how great the technology is, there will st ill be some flaws and problems. The existence of computer viruses revolutionized the way the computer works and what type of security measures are supposed to be taken to prevent this serious problem.
| PowerPoint PPT presentation | free to download
Internet Basics 2 A presentation of the Elmhurst Public Library Frames Some pages are actually more than one page combined together. These pages are called frames.
| PowerPoint PPT presentation | free to download
OAAIS Enterprise Information Security. Security Awareness, Training & Education (SATE) Program ... Masquerade as legitimate programs, but hide more sinister activities ...
| PowerPoint PPT presentation | free to view
Sir Arthur Conan Doyle's detective, Sherlock Holmes, was an expert in cryptography. The Adventure of the Dancing Men, involves a cipher consisting of stick men, ...
| PowerPoint PPT presentation | free to download
They cause the sea to glow when the water is disturbed, perhaps confusing would ... are colorful gastropods known as the 'slugs of the sea' because they lack shells. ...
| PowerPoint PPT presentation | free to view
... custom compiled program that will decompress and launch the embedded programs. ... the embedded files in it are automatically decompressed and launched. ...
| PowerPoint PPT presentation | free to view
... yeast If the answer is not here, the dog needs to see a vet Dog Skin Disease Dorsal Skin Necrosis Open wounds or scars over the back are not uncommonly seen ...
| PowerPoint PPT presentation | free to download
Cindy's Funny #1. Cindy's Useless Fact Of The Week ... FREE!!!---Jokeworm - PPS. PowerPoint Slide Shows are the latest Craze on the net. ...
| PowerPoint PPT presentation | free to view
Title: PowerPoint Presentation Last modified by: Andy Wang Created Date: 1/1/1601 12:00:00 AM Document presentation format: On-screen Show Other titles
| PowerPoint PPT presentation | free to download
The virus code will be executed when the infected program is executed. ... Viruses are a type of malicious software, but malware also includes many other ...
| PowerPoint PPT presentation | free to view
Information Technology Security Presented by: Mike Russo, PMP , CISSP, CFE, CGEIT State Chief Information Security The Agency for Enterprise Information Technology
| PowerPoint PPT presentation | free to view
| PowerPoint PPT presentation | free to download