The public streets and highways of the internet have become like neighborhoods where it is no longer - PowerPoint PPT Presentation
Title:
The public streets and highways of the internet have become like neighborhoods where it is no longer
Description:
Phishing attacks: use e-mails that often appear to come from a legitimate e-mail ... Hoax letters: http://hoaxbusters.ciac.org ... – PowerPoint PPT presentation
Number of Views:97
Avg rating:3.0/5.0
Title: The public streets and highways of the internet have become like neighborhoods where it is no longer
1
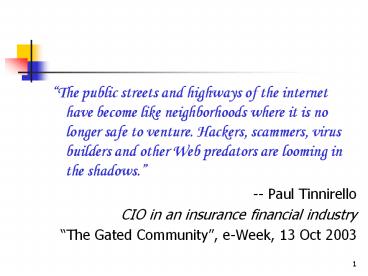
- The public streets and highways of the internet
have become like neighborhoods where it is no
longer safe to venture. Hackers, scammers, virus
builders and other Web predators are looming in
the shadows. - -- Paul Tinnirello
- CIO in an insurance financial industry
- The Gated Community, e-Week, 13 Oct 2003
2
- Computer Crimes
- An information session for participants in the
57-201 Introduction to Forensic Science course - Akshai Aggarwal
- School of Computer Science
3
Flow of the session
- Historical perspective 4-14
- Threats and Attacks
- Threats 18-21
- Types of Attacks 23-30
- Technology of defence 32-50
- Laws and group Efforts in Canada 51
- A couple of general ideas, in conclusion
- Note Terminology may be explained, as the need
arises.
4
Historical Perspective Terminology
- 1960s and 1970s
- Hacker a positive term
- A Hacker An expert, knowledgeable about
programming and operating systems - 1970s onwards
- Hacker a term, which progressively became more
negative. - A Hacker Someone using computers without
authorization - .
- .
- Hacker Someone committing crimes by using
computers
5
Types of Non-authorized Users
- Hacker people who access a computer resource,
without authorization - Crackers a hacker who uses his or her skills to
commit unlawful acts, or to deliberately create
mischief - Script Kiddies a hacker who downloads the
scripts and uses them to commit unlawful acts, or
to deliberately create mischief, without fully
understanding the scripts. - Vandals
- Referencehttp//www.e2chameleon.btinternet.co.uk/
hacking.htm
6
Terminology of Hacking
- Eavesdropping or Snooping (also called passive
wire-tapping) - Active wire-tapping or man-in-the middle attack
- Dumpster Diving colloquial for looking through
all the easily available material before an
actual intrusion into a system
7
The Global Net A Virtual Intelligent
Global System
- 2 Sept 1969 LEN KLEINROCKS Lab at UC,LA
1971 15 Nodes
23 Hosts - 1973 BOB METCALFES thesis on
ETHERNET at Harvard - 1974 TCP CERF BOB KAHNS paper
- 1983 DoD Official Protocol.
- 1989 Hypertext WWW at CERN by
- Berner Lee
- Then came the BROWSERS MOSAIC NCSA
- and the WWW
8
Security TechnologiesA little history of an
ancient art The first printed book on
cryptology
- Johannes Trithemius, an abbot in Spanheim One
of the founders of cryptology - The first printed book of cryptology titled
Polygraphiae Libri Sex in German language in
1518 by Johannes Trithemius,published after the
death of the writer. - (The title means -Six Books of Polygraphy)
9
A little history (continued)
- Earlier in 1499 he had written a 3-book
- Steganographia, (meaning covered writing)
- which was circulated privately
- was published in 1606.
- The first two books about cryptology.
- But the third book could not be understood,
without understanding the encoding that he had
used.
10
A little history (continued) A
challenge for a cryptanalyst
- In the third book, which was considered to be
incomplete, Trithemius explained why he had made
it hard to understand - This I did that to men of learning and men
deeply engaged in magic, it might, by the Grace
of God, be in some degree intelligible, while on
the other hand, to the thick skinned
turnip-eaters it might for all time remain a
hidden secret, and be to their dull intellects a
sealed book forever.
11
Ban, what you dont understand.
- The third book banned in 1609, ostensibly
because it explained how to employ spirits for
sending secret messages. - The challenge - of deciphering the book met by
three persons in 500 years - 1676Wolfgang Heidel, the archbishop of Mainz,
Germany, claimed to have deciphered the third
book of Trithemius. - But his discovery was stated in a secret code
of his own. So nobody knew whether Heidel had
understood the book.
12
A little history Deciphering the third book
of Trithemius
- 1996Thomas Ernst, Prof of German at La Roche
College, Pittsburgh published a 200-page
German-language report in a small Dutch journal,
Daphnis. - WIDELY KNOWN SOLUTION spring 1998 Jim Reeds of
AT T labs solved the riddle of understanding
the third book independently. - He did not know of the earlier work of Ernst.
- Trithemius work basically simple Ernst took two
weeks and Reeds took two days to understand it. - Both Ernst and Reeds, separately, deciphered
Heidels work and found that Heidel had been able
to decipher Trithemius third book.
13
The first attack
- The Internet Worm (Nov 1988)
- Morris, a graduate student at CMU released a
program on the internet - utilized a security hole in the mail receipt
software - automatically replicated itself locally and to
remote machines - affected a wide class of machines and effectively
shut down internet for 1-2 days. - Cost estimate to fix 5 million
14
The first conviction
- Mitnick and Shimomura (Christmas 1994)
- Used SYN flooding and TCP Hijacking to connect
to Shimomuras home machine. - Stole copies of 1000s of files including
specialized computer security software modified
log files to remove signs of entry. - Shimomura found out about the entry and informed
FBI.
15
.there will be more security breaches,
says Schneier
- As more of our infrastructure moves online,
- as more things, that someone might want to access
or steal, move online . - As our networking systems become more complex
.. - As our computers get more powerful and more
useful..
16
Common attacks on banks
through Internet
- Losses due to attacks
- "The major banks don't want to divulge the amount
of losses. But just to give one example, a major
Australian bank has put several million dollars
in reserve since August 2003 to cover damages due
to Internet frauds. Dave Jevans, eWeek, Dec
2003
17
Causes of Security Problems on Internet
- Internet Technology was developed based on trust
- Security features added, as different types of
attacks are mounted. - Users bother about ease of use and not about
security
18
Security Threats
- RFC 1244 identifies three distinct types of
security threats associated with network
connectivity - Unauthorized access
- A break-in by an unauthorized person.
- Break-ins may be an embarrassment that
undermine the confidence that others have in the
organization. - Moreover unauthorized access ? one of the
other threats-- disclosure of information or - --denial of service.
19
Classification of Security Threats
Reference RFC 1244
- Disclosure of information
- disclosure of valuable or sensitive information
to people, who should not have access to the
information. - Denial of service or Degradation of service
- Any problem that makes it difficult or impossible
for the system to continue to perform productive
work. - Do not connect to Internet
- a system with highly classified information,
or, - if the risk of liability in case of disclosure
is great.
20
Brent Chapmans Three Categories of
Security Threats
- Brent Chapmans Classification
- Confidentiality
- Of data
- Of existence of data
- Of resources, their operating systems, their
configuration - Of resources used, in case the resources are
taken on rent from a service provider
21
Information Security Threats
Chapmans Classification (contd.)
- availability A DoS attack may disrupt
- availability of a service, or
- availability of data
- integrity
- Of data
- Of origin
- Once someone has gained unauthorized access
- to a system, the integrity of the information on
- that system is in doubt.
22
Loss Breakdown
Reference Jim Alves-Foss , Center for Secure
and Dependable Systems, Univ of Idaho,
http//www.cs.uidaho.edu/jimaf/cs442/crime-talk.p
pt
23
Types of Attacks
- Attacks on computer systems using the computers
- Web-site defacement or
- Revealing the data to unauthorized persons/theft
of sensitive information/ stealing information
having Intellectual Property Rights - like
- stealing credit card numbers
- bank frauds or
- Damage to data
- through
- Hacking or
- Virus/Worms
24
Types of Attacks continued
- Hoax Letters Examples
- Malicious code (viruses and trojan horses)
- Urban myths
- Scam letters to entrap the receiver
- Internet gambling
- Internet Pornography/ stalking
- Link Flooding
- Packet Intercepting, Password Sniffing
25
Types of Attacks
- propagate false routing entries (black holes
and sink holes, www.citibank.com,
www.mybank.az) - domain name hijacking
- Phishing attacks use e-mails that often appear
to come from a legitimate e-mail address and
include links to spoofed Web addresses. The
receiver responds to the link, which takes the
receiver to a site, other than what the receiver
thinks he is going to. (announced by MS on 16 Dec
2003, as a problem with Internet Explorer).
26
Anti-Phishing.org
- A Web site www.antiphishing.org,, for reporting
incidents, set up by a group of global banks and
technology companies, led by Secure-messaging
firm Tumbleweed Communications Corp - Fast Response required The Web sites designed
for collecting personal information in phishing
attacks are often alive for a day only. - Example Dec 2003The e-mail appeared to come
from the U.K. bank NatWest. - Anti-Phishing.org tracked the IP address to
a home computer in San Francisco. - But a clear case of spoofingthe mail was
relayed from a hijacked computer (called a zombie)
27
An Example time-to-market for Internet Security
products
- 16 December, 2003 Discovery of the problem of
Phishing - 5 January 2004 Announcement of development of a
new Anti-phishing service by Netcraft, of Bath,
England. - Netcraft says that the service is mainly for
banks and other financial organizations
28
Other Computer Crimes
- Spoofing or Masquerading of a host or a
service-provider (Distinguish it from Delegation) - Repudiation of origin or of creation of some file
- Denial of receipt
- Usurpation unauthorized control
- Data Diddling (To enter false data intentionally)
29
- To be an effective Information Warrior,
individuals need superior computer skills, as
well as an in-depth understanding of information
technology architectures, protocols and
processes. - --- Michael
Erbschloe - author of Information Warfare How to Survive
Cyber Attacks
30
General Strategies for security
- encrypting sensitive data
- reduce size of target
- disable unneeded services
- limit access of attacker to target systems
- hardening the OS and applications
31
- It is insufficient to protect ourselves with
laws we need to protect ourselves with
mathematics. - ---Bruce Schneier
- in Applied
Cryptography
32
CRYPTOGRAPHY
- Cryptography (from two words in Greek) means
secret writing. - Cryptoanalysis breaking of a cryptographic code
- CRYPTOGRAPHY process data into unintelligible
form, - reversibly/irreversibly
- without data loss
- usually one-to-one in size /compression
33
Cryptography
- Services, provided by cryptographic tools
- Encoding information into a form which makes the
information unintelligible to an unauthorized
person - integrity checking no tampering
- authentication not an impostor
- Encryption or Enciphering
Encryption Algorithm
Ciphertext
Plaintext
Key
34
Encryption
- Two types of Encryption Algorithms
- Reversible
- Irreversible
- Two types of Keys
- Symmetric
- Assymetric
35
Reversible Encryption
- Reversible ENCRYPTION
- cleartext ENCRYPTION DEVICE
-
encryption key - cleartext
- can be used only when the same type of encryption
software/equipment is available at both the ends
ciphertext
Decryption key
Decryption Device
36
Decryption
- Decryption or Deciphering
Decryption Algorithm
Plaintext
Ciphertext
Key
37
Cryptographic Hash Functions (H)
- H A transformation One way
- m variable size input
- h hash value a fixed size string,
- also known as message digest or fingerprint or
compression function.
H(m)
m
h
38
Message Digest (recapitulation)
Variable Length Message
Fixed Length Digest
Hashing Algorithm
39
Secret Key/ Symmetric Cryptography
- Simpler and faster (than ?) and, of course,
secure - For Integrity check, a fixed-length checksum for
the message may have to be used CRC not
sufficient - Cyclic Redundancy Check
40
Symmetric Key Encryption
- Also called Private/Secret key Encryption
- Sender-end
Message by sender
Encrypted Message
Pr-key
Internet
Message at receiver
Pr-key
Encrypted Message
Receiver-end
41
public-key cryptography (continued)
42
Asymmetric Key Encryption
- Also called Public key Encryption
A
Bs public
Encrypted Message
Message
key
Internet
Bs private
Encrypted Message
Message
key
B
43
public-key cryptography (continued)
- Data transmission private key(d), public key (e)
44
public-key cryptography (continued)
- Applications and Advantages
- Storage for safety use public key of trusted
person - Secret vs. Public Key system
- secret key system needs secret key for every
pair of persons, that wish to communicate - n users ? n(n-1)/2 keys
- public key system needs two keys for every
person, who wants to communicate. - n users ? 2n keys
45
Digital certificate for getting
Public Key reliably
- A digital certificate from a trusted party may
contain - The name of a person
- His e-mail address
- His public key
- The recipient of the encrypted certificate uses
the public key of the Certification Authority to
decode the certificate. - Examples of CAs www.verisign.com or
www.thawte.com (Verisigns liability limited to
100 only!) - Standard for certificate X.509
46
Digital signatures
- Digital Signatures A is to sign a Msg and send
it to B
B
Decode digest using Public key of A
Msg
Msg Encoded Digest
Msg Encoded Digest
A
Digest Algorithm
Digest
Digest Algorithm
Msg
Encoding using Private key of A
Digest
Compare
47
Laws and Group Efforts in Canada
- No separate cyberspace law in Canada
- But the Canadian Criminal Code and the Canadian
Human Rights Act apply in cyberspace. - The Internet Protection Portal, established by
the Canadian Association of Internet Providers
(CAIP) an on-line window to resources for a user
to safeguard the Internet experience. - Media Awareness Network (MNet) supports media
education in Canadian homes, schools and
communities.
48
Birthday paradox
- A result from probability theory Consider an
element that has an equal probability of assuming
any one of the N values. The probability of a
collision is more than 50 after choosing 1.2vN
values.
Function
Random input
One of k equally likely values
The same output can be expected after 1.2k1/2
inputs. Thus in a group of 23, two or more
persons are likely to share the same birthday.
(Put k 365) Birthday attacks are used to find
collisions of Hash functions
49
Example of a Birthday Attack
- Assume
- A 64 bit key
- The first statement in a message is always the
same. - A hacker
- listens to and stores all encrypted messages.
- When the FIRST encrypted sentence turns out to be
the same, he replaces the rest of the new message
by the old message, that he has in his memory. - By Birthday Paradox, this is likely to happen
after 232 transactions.
50
Cryptography vs. Steganography
- Cryptography uses techniques like
transpositions and substitution to make a message
unintelligible - Steganography hides the existence of the
method. - Cryptography provides privacy. Steganography
provides secrecy.
51
Hiding a message in a picture
- Described by Wyner in Byte
- Kodak photo CD resolution of 2048x3072 pixels.
- Each pixel 24-bit RGB color information.
- Modify the last bit (out of 8 bits) for each
color. - Amount of data that can be hidden in a single
picture - 2048 30723 2.359296 Mb about 300,000B
- 106
- If four bits of intensity for each of the three
colors RGB are altered ? 1.5 text characters
hidden in each pixel of the photo. - A 640x480 pixel image ? can store over
400,000 characters, equal to a whole book.
52
Steganography Hiding Messages
Example of a Laser printer
- Another example Laser printers can adjust
spacing of lines and characters by less than
1/300th of an inch. - To hide a 0, leave a standard space.
- To hide a 1, leave 1/300th of an inch more than
usual. - Varying the spacing over an entire document can
- hide a short binary message that is undetectable
- by the human eye.
- The hidden message will be carried by every
photocopy of the document also.
53
To Intrusion Detection Analysts
- Folks!
- You are the trackers of the 21st century.
- The signs are there, plain as day. It is up to
you to find them and give the interpretation. - Stephen Northcutt et.al.
54
References
- The Trithemius riddle 1. Thomas (Penn) Leary,
Cryptology in the 16th and 17th Centuries,
Cryptologia, July 1996, available at
http//home.att.net/tleary/cryptolo.htm - 2. http//www.post-gazette.com/healthscience/19980
629bspirit1.asp - 3. Gina Kolata, A Mystery Unraveled, Twice, The
New York Times, April 14, 1998, pp. F1, F6,
available at http//cryptome.unicast.org/cryptome0
22401/tri-crack.htm - Hoax letters http//hoaxbusters.ciac.org/