Worst Password Of The Year PowerPoint PPT Presentations
All Time
Recommended
Despite all warnings from cybersecurity experts, many people still don’t take serious action to choose strong passwords they use to log into apps and websites. SplashData, the company that makes password manager SplashID, studied more than 5 million leaked passwords from recent breaches and found that many of the commonly used passwords. Here are some of the worst password of 2018 https://www.thethreatreport.com/some-of-the-worst-passwords-of-2018/
| PowerPoint PPT presentation | free to download
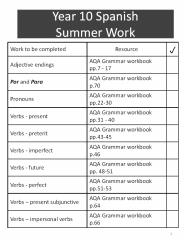
Year 10 Spanish Summer Work Work to be completed Resource p Adjective endings AQA Grammar workbook pp.7 - 17 Por and Para AQA Grammar workbook p.70 Pronouns
| PowerPoint PPT presentation | free to download
Identifying Worst Information Technology Practices Where s the risk? Why examine worst-practices Occur in many organizations Practiced in the name of efficiency ...
| PowerPoint PPT presentation | free to download
ICT enables new media voices to emerge: Weblogs, Drudge Report ... ICT enables watchers to report sightings into online database, and visualize migration patterns ...
| PowerPoint PPT presentation | free to view
'Tomorrow Never Dies James Bond' Password: TwNrDs007. 30. Major threats to password ... Hold 100 characters. Paper thin stamp size. 34. Problem with Physical Tokens ...
| PowerPoint PPT presentation | free to view
As a professional wordpress development agency, we develop hundreds of WordPress websites every year. Which is why we have to take special measures to address the problem of WordPress security and equip you with workable solutions that will prevent hackers from peeking and tweaking in your website.
| PowerPoint PPT presentation | free to download
Eldad Lieberman is a chief in a spot of online business for numerous years with strength and forms an enormous list of consumers boosting his net worth over 7 stats.
| PowerPoint PPT presentation | free to download
Upcoming: Quiz Friday, Nov 3 on EFP chapter 11&12 Course evaluations: October 29 through November 20. Go to wku.evaluationkit.com and use your WKU NetID and password.
| PowerPoint PPT presentation | free to download
There have been numerous stories and viral social media posts since the COVID-19 outbreak revealing some of the worst remote security blunders, ranging from either the potentially crippling to the easily inconsequential to the bizarre
| PowerPoint PPT presentation | free to download
email passwords and sysinfo ixltd@postone.com. Scan Types. Vertical Scan ... Normally, before compromising hackers need to use scan to find out venerability ...
| PowerPoint PPT presentation | free to download
... Under new HIPAA laws we must notify patients and the federal government when we have a breach of patient information; ... PASSWORDS HIPAA Security Awareness: ...
| PowerPoint PPT presentation | free to download
In recent years, Conversion Rate Optimization (CRO) has gained even more popularity across various online industries. Probability, it’s going to be the most prominent leverage point for any business, in 2017.
| PowerPoint PPT presentation | free to download
Password protected screensaver. Log on using administrator account ... Beware the 'free / trial' trap. Separation 'Don't put all your eggs in one basket' ...
| PowerPoint PPT presentation | free to view
In recent years, the retail and hospitality industries have been rocked with data breaches with point of sale malware becoming increasingly common. Among several POS hardware available in-store, digital cash registers are often the most common target of malware designed by hackers to steal important data like credit card information.
| PowerPoint PPT presentation | free to download
... which may be replaced every year to get higher computing power. If ... desktop configuration management proactive probing for vulnerabilities ...
| PowerPoint PPT presentation | free to download
Requires three shared secrets between RADIUS client & server. If KEK and MAC key are based on passwords, they are susceptible to offline ...
| PowerPoint PPT presentation | free to download
Four year integrated primary care demonstration project initiated in 2000 ... position to supplement the doctor- patient dyad in order for it to be successful ...
| PowerPoint PPT presentation | free to view
Nonlinear -- May require a creative leap ... For 20 years, it's been almost ready' Human conversation requires a lot of the listener ...
| PowerPoint PPT presentation | free to view
People are deceived into giving them up. People share passwords with friends. People use software to steal them. People watch other ... Most troubling ...
| PowerPoint PPT presentation | free to view
Are you being prompted to login several times to use different application? If yes then do read further to reduce the password fatigue and save your precious time by quickly logging in desired application.
| PowerPoint PPT presentation | free to download
What's the worst that can happen and how can you make sure it doesn't ... someone else help him but he disagreed: the website was his personal project and ...
| PowerPoint PPT presentation | free to view
Unlike some other business continuity scenarios, a pandemic ... Worst pandemic in history, killing more than 50 million, perhaps as many as 100 million. ...
| PowerPoint PPT presentation | free to view
The tech world tends to proceed from one era to another in a roughly 10-15 year cycle. So we had the PC era from the 1980s to the mid-1990s, followed by the internet and world-wide web era, and then the post-2007 (iPhone) mobile era.
Kinsh has expert wordpress web developers in Sydney having average experience of more than 4 tears and have developed websites for companies and organizations across varied domains. More info - https://bit.ly/2IIkasT
| PowerPoint PPT presentation | free to download
The Changing Landscape: External Drivers, Risks, and Rewards for Inter-boundary Authentication Jack Suess 2/8/06
| PowerPoint PPT presentation | free to view
(Compensation comparison) UAL. Trade ya some apples for some of ... For those who've asked.... That's a joke :-) REVISED 09-14-02 ... Construction ...
| PowerPoint PPT presentation | free to view
Dragonfly Technologies can assist in analysing potential savings associated with ... Dragonfly Technologies Pty Ltd. Branko Ninkovic - Director. Tel 61 2 9566 1292 ...
| PowerPoint PPT presentation | free to view
Office of the Information Commissioner www.oic.qld.gov.au Identity theft do s and don ts Who pays the ferryman? If your Westpac account is compromised as a ...
| PowerPoint PPT presentation | free to view
You might have some doubt related to your WordPress website security, and that’s why you Google for the best WordPress security practices.
| PowerPoint PPT presentation | free to download
Title: PowerPoint Presentation Author: Mark Minasi Last modified by: mcohodas Created Date: 4/6/2003 2:20:42 PM Document presentation format: On-screen Show
| PowerPoint PPT presentation | free to download
Is in your bedroom. Your parents need to: ... Web Cams. 1.TALK TO YOUR PARENTS RIGHT AWAY!!! 2. CHECK OUT SOME WEBPAGES FOR TIPS AND HELP. ...
| PowerPoint PPT presentation | free to view
The power of computers is information storage and processing ... as McAfee or Trendmicro; or with multiple programs such as AVG with Ad-Aware. ...
| PowerPoint PPT presentation | free to view
Title: Descriptive Analysis Map Progress Author: DDuBois Last modified by: DDuBois Created Date: 10/27/2003 9:34:28 PM Document presentation format
| PowerPoint PPT presentation | free to view
models and integrates consumers' preferences into medical information systems. Medical Informatics initially focused on providers and institutions then applied ...
| PowerPoint PPT presentation | free to view
... for traditional units, LFL groups/posts, and Eagle Scouts. ... BSA Stock Photos and Logos. BSA Report Repository. ProSpeak. The Briefcase. Flash Page ...
| PowerPoint PPT presentation | free to view
Adjustment- to the social and intellectual world of college ... About 80 percent of graduating college seniors now have done a paid or unpaid ...
| PowerPoint PPT presentation | free to download
Attend this upcoming webinar to learn about updated FDA rules and regulations of Lab Development Diagnostic Tests, LDT and labeling, marketing practices.
| PowerPoint PPT presentation | free to download
Navigating College Financial Aid Program Analysis Dr. Herm Davis 301-548-9423 hdcfaces@comcast.net www.drhermdavis.com
| PowerPoint PPT presentation | free to download
Phone victim, pretend to be DIT (phishing) ... Algorithms based on mathematics, especially number theory ... (characters) into other bytes using a lookup table ...
| PowerPoint PPT presentation | free to view
We explain the real reasons that could convince you for mobile repair and the best doorstep mobile repair! One way to demonize repair and make sure everyone is concerned. Read this PPT to know more.
| PowerPoint PPT presentation | free to download
This PPT discusses the increasing data breach incidents have enhanced the importance of CIOs and CISOs in the digitally transforming organizations, as they are responsible for implementing a successful application security testing strategy.
| PowerPoint PPT presentation | free to download
Here’s how you can get the right mix of security and usability in your apps; effective tips by Enterprise app development team at Helios Solutions.
| PowerPoint PPT presentation | free to download
ELEC5616 computer and network security matt barrie mattb@ee.usyd.edu.au
| PowerPoint PPT presentation | free to view
| PowerPoint PPT presentation | free to view
The working party also had representatives of the Housing Corporation, ACSCO ... Who might have ideas we could learn from. What targets should we set to raise our game ...
| PowerPoint PPT presentation | free to view
white versions of pages. 12. Meteorological & Emissions Descriptive Analysis ... Flow in response to high pressure system along Canadian border. 55 ...
| PowerPoint PPT presentation | free to view
Need to add to map. 2002 'Interim' Emissions Inventories ... Assist us in the general and detailed description of the meteorological setting of each site ...
| PowerPoint PPT presentation | free to view
Why is this different than other retirements? Why or why not upgrade? ... 2003 has an advantage in that it's a trifle more flexible ...
| PowerPoint PPT presentation | free to download
... wage data) and peer grouping. No data changes can be ... New exogenous variables as predictors resulted in new peer grouping factors, models and results. ...
| PowerPoint PPT presentation | free to view
Use tools to find network security weaknesses. Guide to Networking Essentials, Fifth Edition ... help prevent spread of malware, every computer should have ...
| PowerPoint PPT presentation | free to view
Virus protection for servers and desktop computers is a must ... One of the most popular VPN solutions for Linux is a free downloadable package called OpenSwan ...
| PowerPoint PPT presentation | free to view
Cyber security experts are in greater demand due to the increased sensitivity of data and protection along with a shift in perspective towards digital security around the world.
| PowerPoint PPT presentation | free to download
... a browser other than Internet Explorer we recommend Firefox ... Why did you block my computer? How do I get it unblocked? We block compromised computers: ...
| PowerPoint PPT presentation | free to view
Institute for the Protection and Security of the Citizen. European Commission ...
| PowerPoint PPT presentation | free to view
Mistakes are the beginning of a new learning phase. Here they are- 25 Most Common mistakes By the WordPress beginners. Now you know them. So, when you build your WordPress website, avoid these mistakes and learn from these mistakes.
| PowerPoint PPT presentation | free to download
... Library. Ben Bederson, Kelly Booth, Alan Borning, Edward Clarkson, Jason Day, Jim Foley, ... Jim Foley, Ed Clarkson. Contents ... Kelly the Killer Robot ...
| PowerPoint PPT presentation | free to view