Aodv PowerPoint PPT Presentations
All Time
Recommended
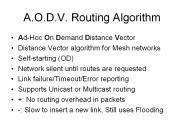
AODV-CE AODV clustering extension node type only one type of node, all the node are equal AODV review AODV review(Continued..) Traffic flooding to whole network Long ...
| PowerPoint PPT presentation | free to download
AODV: Introduction Reference: C. E. Perkins, E. M. Royer, and S. R. Das, Ad hoc On-Demand Distance Vector (AODV) Routing, Internet Draft, draft-ietf-manet-aodv ...
| PowerPoint PPT presentation | free to download
http://users.ece.gatech.edu/~cktoh/workshop.html. Forgetting sequence numbers. Suppose A D via B, C D via B. Suppose B reboots and forgets everything ...
| PowerPoint PPT presentation | free to download
military actions. firefighter operations. autonomous manifesting. real-time ... from civilian activities to military operations. from indoors to outdoors ...
| PowerPoint PPT presentation | free to view
Pirzada, A.A.; McDonald, C,'Secure Routing ... Detection of fabricated routing messages. To fabricate a routing message session key needs to be compromised. ...
| PowerPoint PPT presentation | free to download
... address fields instead of 32-bit. Uses new way to keep track of broadcasts. Using fragment offset id no longer works. BPI == MD5 (non-mutable IPv6 Packet Data) ...
| PowerPoint PPT presentation | free to download
Prefix Sz. Unreachable Destination IP Address (1) Unreachable Destination Sequence Number (1) ... Collection State Overhead ... Same as Collection: ...
| PowerPoint PPT presentation | free to view
Title: Ad Hoc Routing Author: jsevy Last modified by: jsevy Created Date: 4/23/2002 2:18:08 PM Document presentation format: On-screen Show Company
| PowerPoint PPT presentation | free to view
Providing multiple paths is useful in mobile wireless networks ... Nodes of the alternate path optionally may not relay salvaged data packets ...
| PowerPoint PPT presentation | free to view
AODV for IPv4. Charles E. Perkins, Elizabeth Royer, Samir Das. IETF 49, San Diego, CA ... More details about nodes with multiple interfaces. Minor typographical ...
| PowerPoint PPT presentation | free to download
Better specification for handling unidirectional links. If a node fails to send RREP_ACK, put it on a blacklist (ignore its RREQs) ...
| PowerPoint PPT presentation | free to download
Title: Ad Hoc Routing Author: jsevy Last modified by: IBM_USER_AJ Created Date: 4/23/2002 2:18:08 PM Document presentation format: On-screen Show (4:3)
| PowerPoint PPT presentation | free to download
Maintain multiple paths learned from a route discovery ... The number of route discoveries dominates the number of probe packets in simulations. ...
| PowerPoint PPT presentation | free to download
Internet Access from anywhere, including ad hoc networks. ... The gateway responds with a I' flagged RREP providing its address and prefix. ...
| PowerPoint PPT presentation | free to view
Indeed, nodes have to use a high level (or extra) network to transmit their location. ... Data are transmitted over the ad hoc network frequency. ...
| PowerPoint PPT presentation | free to view
AODV - CMU Monarch extensions, 12/07/2000. With link-layer failure ... ns-2 with CMU Monarch extensions. WaveLAN IEEE 802.11 MAC with rate 2Mb/s and range 250m ...
| PowerPoint PPT presentation | free to view
Setup reverse path. A node records the address of the neighbor sending RREQ ... Unicast RREP (Route reply) back to the reverse path ...
| PowerPoint PPT presentation | free to view
Mobility causes route changes. AODV. Route Requests (RREQ) are ... Adds address and power differential for such neighbours. When a node receives a Hello message ...
| PowerPoint PPT presentation | free to view
'Continuous', which means that the behavior of avatar X at time t 1 can be ... When an avatar position (ADU) is missing at the time we compute a bucket, simply ...
| PowerPoint PPT presentation | free to view
RREP contains sequence number, hop-count field (initialized to 0) Will be sent along 'reverse' path hops created by intermediate nodes which forwarded RREQ ...
| PowerPoint PPT presentation | free to view
Make up the AODV protocol specification by the reference papers. Programming ... ( CrossBow provides lots of tools, link Surge-View, on their website. ...
| PowerPoint PPT presentation | free to view
Update reverse route (to source) when receiving RREQ ... M send m1(RREQ) with high SN(A) to take over b1 and divert reverse route (C to M) ...
| PowerPoint PPT presentation | free to view
Phung Huu Phu, Myeongjae Yi, and Myung-Kyun Kim. Network-based Automation Research Center and ... CICA, Sophia Antipolis, French Riviera, La Cote d'Azur, FRANCE ...
| PowerPoint PPT presentation | free to download
OPNET Modeler is a network simulation software tool 80% of the Fortune 100 use OPNET s Performance Management solutions. Rowan received a license grant from OPNET ...
| PowerPoint PPT presentation | free to download
MANET Routing Protocols. Evaluation Approach. Results and Interpretation ... Mobile Ad-hoc Networks (MANETs) can be used for many applications since they are: ...
| PowerPoint PPT presentation | free to view
... route discovery and maintenance Record next hop and when unavailable it initiate route maintenance Secure AODV SAODV Add signature extensions to AODV ...
| PowerPoint PPT presentation | free to download
Conclusion. 8. Abstraction. A finite set of predicates defines the abstraction ... Conclusion. 20. AODV Example. Ad-hoc On-demand Distance Vector (AODV) routing ...
| PowerPoint PPT presentation | free to view
AODV: Ad-Hoc On-Demand Distance Vector Routing Ad-hoc On-Demand Distance Vector Routing Charles E Perkins, Elizabeth M Royer Proc. 2nd IEEE Wksp.
| PowerPoint PPT presentation | free to download
AODV (www.ietf.org/internet-drafts/draft-ietf-manet-aodv-13.txt) OLSR (www.ietf.org/internet-drafts/draft-ietf-manet-olsr-10.txt ...
| PowerPoint PPT presentation | free to download
NIIT-NUST * We need an Intrusion Detection system in the network ... Security Enhancements in AODV protocol for Wireless Ad Hoc Networks Intrusion Detection Model ...
| PowerPoint PPT presentation | free to view
Paul Fong: Wireless AODV Routing for sensor networks. Nirmala Belusu: Wireless Network Security ... Invite speakers from Industry such as Innerwall and AFA? ...
| PowerPoint PPT presentation | free to download
Formal verification of distance vector routing protocols Routing in a network Outline RIP (Routing Information Protocol) Internet routing protocol AODV (Ad-hoc On ...
| PowerPoint PPT presentation | free to download
Outline of the Talk Characteristics of Ad-Hoc Networks Issues in Multicast Routing AODV Tree-based Multicast Routing MCEDAR Reliability ... unicast routing protocol.
| PowerPoint PPT presentation | free to download
We instrumented simulation code for AODVv0 supplied by the CMU Monarch Project. ... Simulation from Monarch uses 50 mobile nodes on 1500x300m grid moving 20 m/s. ...
| PowerPoint PPT presentation | free to download
Many routing messages are propagated unnecessarily. Gossip ... Optimization of Gossip (GOSSIP2 and GOSSIP3). Integrate Gossip with AODV. 25. Thank you! ...
| PowerPoint PPT presentation | free to view
Implementation of Collection Tree Protocol in QualNet ... the performance with AODV System Design and ... Implementation of Collection Tree Protocol in ...
| PowerPoint PPT presentation | free to download
Distance Vector algorithm for Mesh networks. Self-starting (OD) ... Sorry Toucan Sam, this guarantees NO LOOPS! AODV Implementations. AODV-UU. Kernel or User mode ...
| PowerPoint PPT presentation | free to download
Intuitively, the higher the difference between n and k, the greater the ... PA-SHORT-DV works with distance vector algorithms such as AODV. ...
| PowerPoint PPT presentation | free to view
scalable routing protocol in resource (memory, power, and bandwidth) ... for data aggregation, energy-aware routing compare performance of VSV vs. AODV and DSR
| PowerPoint PPT presentation | free to download
Challenges of Secure Routing in MANETs: A Simulative Approach using AODV-SEC Analysis of a technical report from Stephan Eichler and Christian Roman, IEEE ...
| PowerPoint PPT presentation | free to download
Ad Hoc On-Demand Distance Vector (AODV) Comparison of Routing Protocols. Packet Delivery Ratio ... http://www.wired.com/news/business/0,1367,56350,00.html. Conclusion ...
| PowerPoint PPT presentation | free to download
Single-scope/Multi-scope/ Geographically Routing Protocols ... Ad Hoc On-Demand Distance Vector outing(AODV) [1] Dynamic Source Routing(DSR) [2] ...
| PowerPoint PPT presentation | free to view
Black list may not be accurate reflection of unidirectional link ... How AODV Uses Black-list to Work on a Unidirectional Network. 8/29/09. CSE890: Independent Study ...
| PowerPoint PPT presentation | free to view
Manet: Mobile Ad hoc Networks. No fixed infrastructure. Mobile nodes. Multi-hop wireless network ... Routing protocol in Manet: AODV DSR DSDV . Target applications: ...
| PowerPoint PPT presentation | free to view
Based on ns Tutorial (IX, XI) and ns manual (Chapter 14) ... TCP(reno, tahoe, vegas, sack) MAC(802.11, 802.3, TDMA) Ad-hoc Routing (DSDV, DSR, AODV, TORA) ...
| PowerPoint PPT presentation | free to view
Based on AODV and TBRPF Utilizes geolocalization information available by external avionics applications Parameter optimization based on the aeronautical ...
| PowerPoint PPT presentation | free to download
Mobile nodes operate as routers Mobile nodes participate in an ad hoc routing protocol Why ... pause time
| PowerPoint PPT presentation | free to download
[Recent security solutions for mobile ad hoc networks. In 'Ad Hoc Networks' IEEE ... [Protecting AODV against impersonation attacks, ACM MC2R, October 2002] ...
| PowerPoint PPT presentation | free to download
Reverse Path Setup in AODV. B. A. S. E. F. H. J. D. C. G. I. K ... Forward links are setup when RREP travels along. the reverse path ...
| PowerPoint PPT presentation | free to view
Signal-Strength-Aware Routing in Ad hoc Networks. Abhinav Gupta. Ian ... Signal-strength-aware AODV is a good choice for ad hoc networks because of low ...
| PowerPoint PPT presentation | free to download
Cluster-based Energy Conservation (CEC) Self-configuring topology formation ... Network lifetime Comparison between CEC, GAF and AODV ...
| PowerPoint PPT presentation | free to download
To introduce students to ad-hoc network and AODV routing protocol ... RT2500-Linux-STA-1.4.6.2/Utility/Raconfig2500. 4. Lab #4: Step 2. Set up an ad-hoc network ...
| PowerPoint PPT presentation | free to download
Linux routing daemon. Based on RFC3561. Source Structure of EUROP. AODV-UU about 200lines. Reusable code : 200/20,000 = 1% Modified only RREQ RREP HELLO message ...
| PowerPoint PPT presentation | free to view
... protocol AODV threats Real time intrusion detection for AD hoc networks RIDAN ... many latter versions were developed like wireless mesh networks, wireless ...
| PowerPoint PPT presentation | free to download
Stateful Routing Schemes SP (Shortest Path) - AODV (Ad hoc ... An RPC Design for Wireless Sensor Networks - Terry D. May, Shaun H. Dunning, Jason O. Hallstrom ...
| PowerPoint PPT presentation | free to download
The diameter of the network is shorter than m hops. Use hash ... WatchDog PathFinder: DSR. SAODV: Digital signature Hash chain, AODV. SEAD: Hash chain, DSDV ...
| PowerPoint PPT presentation | free to view